Call a Specialist Today! 844-294-0778
PA-7000 Series
PA-7500
The platform standard for hyperscale security, powered by the FE400 ASIC with over 1.5 Tbps of App-ID performance and 440M concurrent sessions.
View pricing Request a quote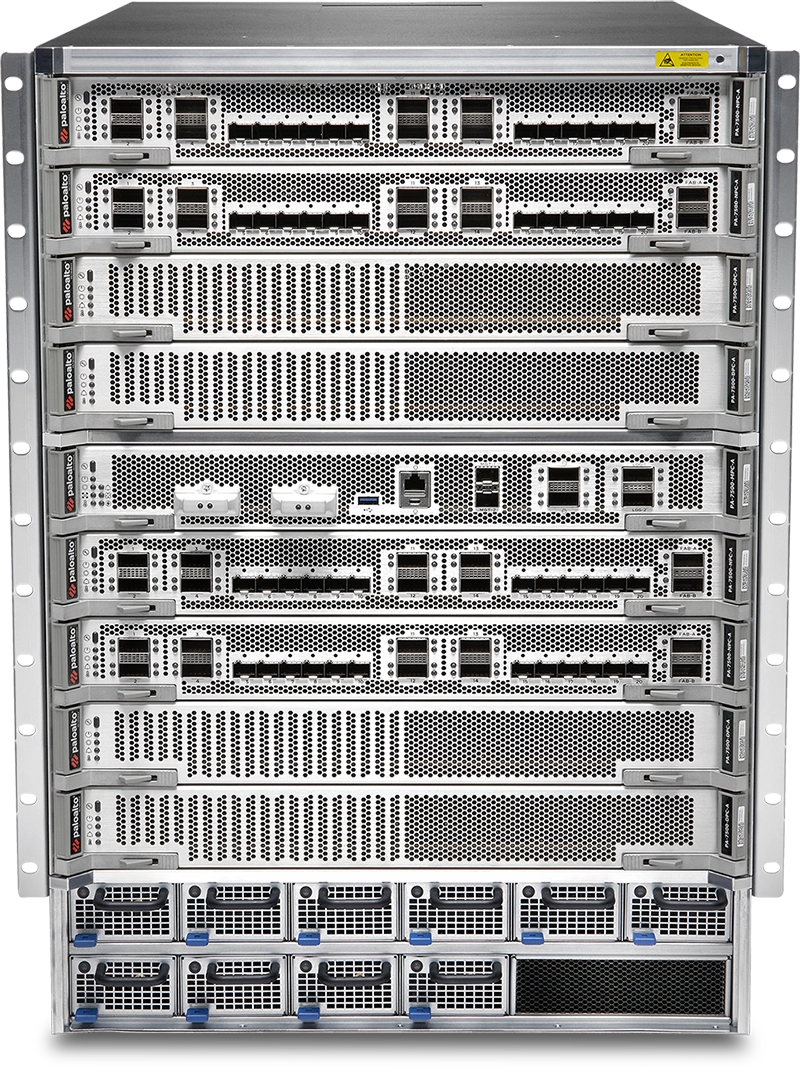
Hyperscale security powered by the FE400 ASIC
The PA-7500 delivers 1,500 Gbps of App-ID firewall throughput with 1,440 Gbps threat prevention and 440M concurrent sessions. Its modular DPC/NPC/MPC/SFC architecture scales across nine card slots to meet the requirements of the largest data centers and service providers.
FE400 ASIC powered
Custom silicon delivers over 1.5 Tbps of App-ID performance with 400M+ concurrent Layer 7 sessions in a single chassis.
Precision AI-powered security
Inline deep learning and ML-based analysis detect and prevent zero-day threats, evasive malware, and command-and-control traffic in real time.
Service provider grade
5G-native security, GTP/SCTP protocol support, and massive session tables serve the most demanding carrier and enterprise data center environments.
Key capabilities
Full Layer 7 inspection
Identifies applications regardless of port, protocol, or encryption, using the application as the basis for security policy decisions.
Cloud-delivered security services
Add Advanced Threat Prevention, WildFire, URL Filtering, DNS Security, IoT Security, and DLP without additional infrastructure.
Native web proxy support
Consolidate firewall and proxy into a single platform with explicit and transparent proxy modes, managed through a centralized policy interface.
Centralized management
Manage configuration, policies, and visibility across all deployments through Panorama or Strata Cloud Manager from a single interface.
Performance summary
| PA-7500 specifications | |
|---|---|
| Firewall throughput (App-ID enabled) | 1,500 Gbps |
| Threat prevention throughput | 1,440 Gbps |
| IPsec VPN throughput | 850 Gbps |
| Max concurrent sessions | 440,000,000 |
| New sessions per second | 7,200,000 |
| Virtual systems (base/max) | 25/225 |
Documentation
PA-7500 datasheet
Complete specifications, performance data, and hardware details for the PA-7500 chassis system.
Download PDFFirewall overview datasheet
Comprehensive overview of PA-Series firewall capabilities and architecture.
Download PDFPricing
Pricing is based on approved deal registration. All figures are subject to change without notice.
