Call a Specialist Today! 844-294-0778
Prisma SaaS Security
Securing SaaS in an AI-Driven World
Prisma SaaS Security, part of Palo Alto Networks Prisma SASE, is the industry's only SASE-native SaaS security solution powered by Precision AI®. It delivers comprehensive visibility, intelligent data protection, and proactive risk mitigation across SaaS, collaboration platforms, and GenAI applications—without disrupting user productivity.
Request a ConsultationWhy SaaS Security
As organizations accelerate SaaS and GenAI adoption, traditional controls struggle to keep pace. Prisma SaaS Security addresses the growing visibility, data protection, and insider risk challenges inherent in modern SaaS environments.
-
Shadow IT and unmanaged GenAI usage
-
Misconfigurations across hundreds of SaaS platforms
-
Sprawling and overexposed sensitive data
-
Increased insider and threat actor activity in collaboration apps
Gain Visibility into a SaaS World Shaped by AI
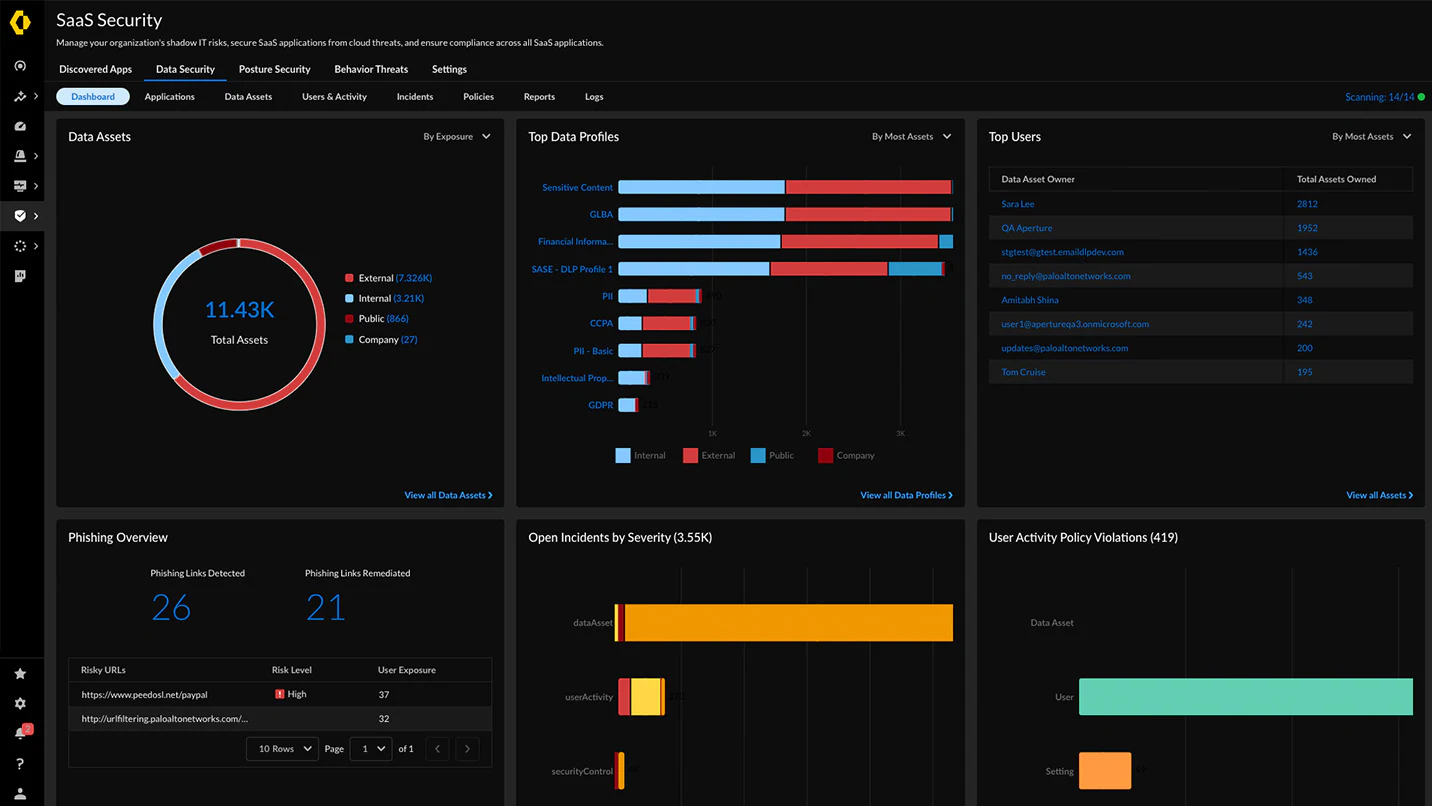
Prisma SaaS Security provides comprehensive discovery and continuous monitoring of all SaaS and GenAI applications across your organization, including shadow IT and unmanaged usage.
Discover All SaaS & GenAI Apps
Identify sanctioned and unsanctioned applications, including GenAI tools like ChatGPT, Gemini, and Microsoft Copilot, across your entire environment.
Monitor User Activity
Track user behavior and application usage patterns to detect risky activities, data exfiltration attempts, and policy violations in real time.
Assess Risk Continuously
Evaluate SaaS and GenAI applications against security, compliance, and business risk criteria to prioritize remediation efforts.
Protect What Matters Most: Your Data
Prisma SaaS Security delivers AI-powered data protection that identifies, classifies, and safeguards sensitive information across all SaaS applications and GenAI platforms.
Advanced Data Loss Prevention (DLP)
- Precision AI-driven classification of structured and unstructured data
- Real-time detection and prevention of data leakage, sharing violations, and unauthorized access
- Contextual policies based on user, application, content, and activity
- Integration with Palo Alto Networks Enterprise DLP for unified protection
Secure Sensitive Data Everywhere
Protect intellectual property, customer data, financial records, and regulated information across SaaS apps, file-sharing platforms, and collaboration tools—automatically and at scale.
Enable Safe GenAI Adoption with AI Access Governance
Empower your organization to leverage the productivity gains of GenAI applications while maintaining security and compliance. Prisma SaaS Security provides AI Access Governance to control and monitor GenAI usage across the enterprise.
Govern GenAI Usage
- Define policies for approved GenAI applications and block unauthorized tools
- Monitor prompts and responses for sensitive data exposure
- Prevent intellectual property leakage through GenAI interactions
Protect Data in GenAI Workflows
- Inspect and redact sensitive information before it reaches GenAI models
- Apply contextual DLP policies based on user role and application
- Ensure compliance with data residency and privacy regulations
Complete GenAI Security: Combine Prisma SaaS Security with AI Access Security for comprehensive protection across managed and unmanaged GenAI applications.
Proactive Risk Mitigation with Continuous Compliance
Prisma SaaS Security continuously monitors your SaaS environment for misconfigurations, compliance violations, and security risks—enabling you to remediate issues before they become breaches.
Security Posture Management
Identify and remediate misconfigurations across SaaS platforms, including overly permissive sharing, weak authentication, and disabled security controls.
- Automated discovery of configuration drift
- Prioritized remediation recommendations
- Continuous compliance monitoring
Compliance Automation
Ensure adherence to regulatory frameworks including GDPR, HIPAA, PCI DSS, SOC 2, and industry-specific requirements with automated policy enforcement.
- Pre-built compliance templates
- Automated audit reporting
- Real-time violation alerts
Third-Party App Risk Assessment
Evaluate OAuth-connected applications for security risks, excessive permissions, and potential data exposure across your SaaS ecosystem.
- Permission analysis and scoring
- Automatic revocation of risky apps
- User and app behavior correlation
User Behavior Analytics (UBA)
Detect anomalous user activities that may indicate compromised accounts, insider threats, or policy violations using machine learning.
- Baseline normal behavior patterns
- Alert on deviations and anomalies
- Risk scoring and investigation workflows
Stop Threats and Malicious Insiders
Prisma SaaS Security leverages Precision AI Security Services to detect and block advanced threats, malware, and malicious insider activity across all SaaS applications.
Advanced Threat Protection
Malware Detection
Inline scanning of files and content to prevent malware distribution through SaaS apps
Phishing Prevention
Block credential phishing and account takeover attempts in collaboration platforms
Ransomware Protection
Detect and prevent ransomware encryption activities across cloud storage
Insider Threat Detection
Identify and respond to malicious or negligent insider activities including data exfiltration, unauthorized sharing, and account compromise.
- Real-time detection of suspicious download and sharing patterns
- Automated response workflows including session termination and access revocation
- Integration with SIEM and SOAR platforms for coordinated incident response
Simplify Management with a Unified, Intelligent Platform
Prisma SaaS Security integrates natively into the Prisma SASE platform, providing unified visibility, policy management, and threat intelligence across your entire security stack.
Single-Pane-of-Glass Management
- Manage SaaS security alongside Prisma Access, SD-WAN, and other Prisma services
- Unified policy engine for consistent enforcement across network and cloud
- Centralized reporting and analytics with customizable dashboards
AI-Powered Operations
- Automated threat detection and policy recommendations powered by Precision AI
- Natural-language troubleshooting and analysis through Strata Copilot
- Reduced alert fatigue with intelligent prioritization and correlation
Seamless Deployment
Deploy SaaS security inline through Prisma Access or via API integration—no agents, proxies, or network changes required. Scale effortlessly as your SaaS footprint grows.

Prisma SaaS Security Datasheet
Download the complete technical overview of Prisma SaaS Security features, capabilities, and deployment options.
Get Started with Prisma SaaS Security
Contact us to learn how Prisma SaaS Security can protect your organization's SaaS and GenAI applications
Prisma SaaS Security is part of the Palo Alto Networks Prisma platform family, delivering comprehensive cloud security and SASE solutions.
