GlobalProtect
Prevent Breaches and Secure the Mobile Workforce
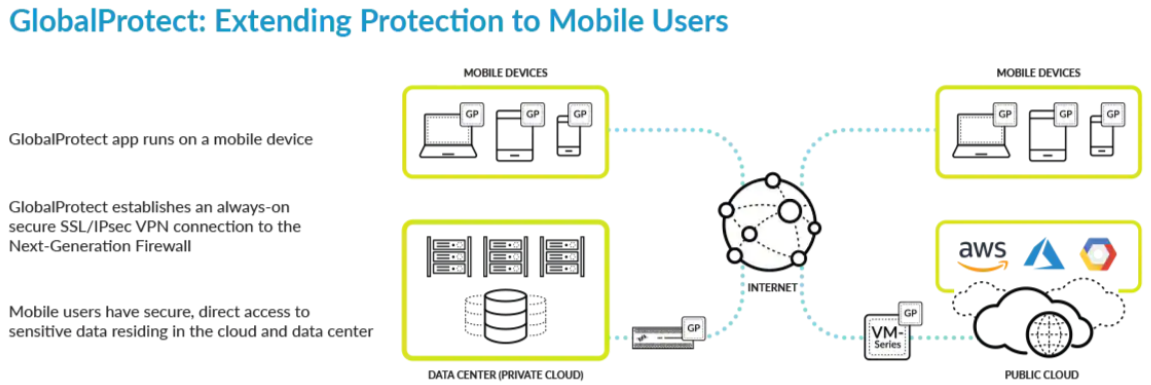
GlobalProtect extends the protection of the Palo Alto Networks Security Operating Platform to the members of your mobile workforce, no matter where they go.
Palo Alto Networks GlobalProtect™ network security for endpoints enables organizations to protect the mobile workforce by extending the Security Operating Platform® to all users, regardless of location. It secures traffic by applying the platform’s capabilities to understand application use, associate the traffic with users and devices, and enforce security policies with next-generation technologies.
Key Usage Scenarios and Benefits
Remote Access VPN
- Provides secure access to internal and cloud-based business applications.
Advanced Threat Prevention
- Secures internet traffic.
- Stops threats from reaching the endpoint.
- Protects against phishing and credential theft.
URL Filtering
- Enforces acceptable use policies.
- Filters access to malicious domains and adult content.
- Prevents the use of avoidance and evasion tools.
- Secures access to SaaS applications.
- Controls access and enforces policies for SaaS applications while blocking unsanctioned applications.
BYOD
- Supports app-level VPN for user privacy.
- Enables secure, clientless access for partners, business associates, and contractors.
- Supports automated identification of unmanaged devices.
- Supports customized authentication mechanisms for managed and unmanaged devices.
Zero Trust Implementation
- Delivers reliable user identification.
- Delivers immediate and accurate host information for visibility and policy enforcement.
- Enforces step-up multi-factor authentication to access sensitive resources.
Inspection of Traffic and Enforcement of Security Policies
GlobalProtect enables security teams to build policies that are consistently enforced whether the user is internal or remote. Security teams can prevent successful cyberattacks by bringing all of the platform’s capabilities to bear:
- App-ID™ technology identifies application traffic, regardless of port number, and enables organizations to establish policies to manage application usage based on users and devices.
- User-ID™ technology identifies users and group memberships for visibility as well as the enforcement of role-based network security policies.
- SSL Decryption inspects and controls applications that are encrypted with SSL/TLS/SSH traffic and stops threats within the encrypted traffic.
- WildFire® malware prevention service automates the analysis of content to identify new, previously unknown, and highly targeted malware by its behavior and generates the threat intelligence to stop it in near-real time.
- Threat Prevention for IPS and antivirus blocks network-based exploits targeting vulnerable applications and operating systems, denial-of-service (DoS) attacks, and port scans. Antivirus profiles stop malware and spyware from reaching the endpoint using a stream-based engine.
- URL Filtering with PAN-DB categorizes URLs based on their content at the domain, file, and page level, and receives updates from WildFire so that when web content changes, so do categorizations.
- File blocking stops the transfer of unwanted and dangerous files while further scrutinizing allowed files with WildFire.
- Data filtering enables administrators to implement policies that can be used to stop the unauthorized movement of data, such as the transfer of customer information or other confidential content.
Secure Access Control
User Authentication
GlobalProtect supports all existing PAN-OS® authentication methods, including Kerberos, RADIUS, LDAP, SAML 2.0, client certificates, biometric sign-in, and a local user database. Once GlobalProtect authenticates the user, it immediately provides the next-generation firewall with a user-to-IP-address mapping for User-ID.
Strong Authentication Options
GlobalProtect supports a range of third-party multi-factor authentication (MFA) methods, including one-time password tokens, certificates, and smart cards, through RADIUS and SAML integration.
These options help organizations strengthen the proof of identity for access to internal data center or software-as-a-service (SaaS) applications.
GlobalProtect has options to make strong authentication even easier to use and deploy:
- Cookie-based authentication: After authentication, you may choose to use an encrypted cookie for subsequent access to a portal or gateway for the lifetime of that cookie.
- Simplified certificate enrollment protocol support: GlobalProtect can automate the interaction with an enterprise PKI for managing, issuing, and distributing certificates to GlobalProtect clients.
- MFA: Before a user can access an application, he or she can be required to present an additional form of authentication.
Host Information Profile
GlobalProtect checks the endpoint to get an inventory of how it’s configured and builds a host information profile (HIP) that’s shared with the next-generation firewall. The next-generation firewall uses the HIP to enforce application policies that only permit access when the endpoint is properly configured and secured. These principles help enforce compliance with policies that govern the amount of access a given user should have with a particular device.
HIP policies can be based on a number of attributes, including:
- Managed/Unmanaged device identification
- Machine certificates present on device
- Device information received from mobile device manager
- Operating system and application patch level
- Host anti-malware version and state
- Host firewall version and state
- Disk encryption configuration
- Data backup product configuration
- Customized host conditions (e.g., registry entries, running software)
Control Access to Applications and Data
Security teams can establish policies based on application, user, content, and host information to maintain granular control over access to a given application. These policies may be associated with specific users or groups defined in a directory to ensure that organizations provide the correct levels of access based on business need. The security team can further establish policies for step-up MFA to provide additional proof of identity before accessing particularly sensitive resources and applications.
Enhanced Troubleshooting and Visibility
GlobalProtect Application Command Center (ACC) widgets, reports, and the new GlobalProtect log provide full visibility into GlobalProtect usage in your deployment. Detailed logging of the connection workflow in stages greatly simplifies troubleshooting of user connection issues. This logging allows administrators to easily identify the stage/event in the connection process where a given user has an issue.
Secure and Enabled BYOD
The effects of bring-your-own-device (BYOD) policies are changing the number of use case permutations that security teams need to support. It is necessary to provide application access to a broader spectrum of employees and contractors using a wide range of mobile devices.
Integration with mobile device management offerings, such as AirWatch® and MobileIron®, can help you deploy GlobalProtect as well as provide additional security measures through the exchange of intelligence and host configuration. Using these in conjunction with GlobalProtect, your organization can maintain visibility and the enforcement of security policy on a per-app basis while maintaining data separation from personal activities to honor the user’s expectations of privacy in BYOD scenarios.
GlobalProtect supports clientless SSL VPN for secure access to applications in the data center and the cloud from unmanaged devices. This approach allows customers to enable secure access for third-party users and employees connecting from BYOD devices by providing access to specific applications through a web interface, both without requiring users to install a client and without setting up a VPN tunnel.
Architecture Matters
The flexible architecture for GlobalProtect provides many capabilities that can help you solve an array of security challenges. At the most basic level, you can use GlobalProtect as a replacement for the traditional VPN gateway, eliminating the complexity and headaches of administering a standalone, third-party VPN gateway.
Options for manual connections and gateway selection enable you to tailor the configuration to support business requirements as needed.
In a more comprehensive deployment for securing traffic, GlobalProtect can be deployed with an always-on VPN connection with a full tunnel, ensuring that protection is always present and transparent to the user experience. Exceptions can be defined for latency-sensitive traffic by application, domain names and routes, or video traffic.
Cloud-Based Gateways
Workforces shift from one location to another, creating changes in traffic load. This is especially true when considering how companies evolve, whether on a temporary basis (e.g., following a natural disaster) or a permanent one (e.g., when entering new markets).
Prisma™ Access by Palo Alto Networks provides a co-managed option for deploying coverage in the locations organizations need, using your security policies. It can be used in conjunction with your existing firewalls, making your architecture adaptable to changing conditions.
Prisma Access supports auto-scaling, which dynamically allocates new firewalls based on load and demand in a given region.
Conclusion
The Palo Alto Networks Security Operating Platform plays a critical role in preventing breaches. Use GlobalProtect to extend the protection of the platform to users wherever they go. By using GlobalProtect, you can get consistent enforcement of security policy so that even when users leave the building, their protection from cyberattacks remains in place.
Download the Palo Alto Networks GlobalProtect Datasheet (PDF).
