Overview:
The VM-Series supports the exact same next-generation firewall and advanced threat prevention features available in our physical form factor appliances, allowing you to safely enable applications flowing into, and across your private, public and hybrid cloud computing environments.
Automation features such as VM monitoring, dynamic address groups and a REST-based API allow you to proactively monitor VM changes dynamically feeding that context into security policies, thereby eliminating the policy lag that may occur when your VMs change.
The VM-Series supports the following hypervisors:
- VMWare ESXi and NSX
- Citrix SDX,
- KVM (Centos/RHEL)
- Ubuntu
- Amazon Web Services
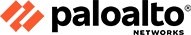
Virtualized Firewalls
As your organization embraces virtualization and cloud initiatives, your
networking, security and virtualization teams have two alternatives when it
comes to protecting the resident mission-critical applications and data from
modern cyber threats. The first alternative is to ignore security all together, not
because it is unnecessary, but because security policy deployment cannot keep
pace with the rate of virtualization changes, oftentimes lagging weeks behind.
The second alternative is to implement traditional security technologies that
are port-bound, which means they lack the ability to identify and control
applications, and they are ineffective at blocking today's modern attacks. Neither
of these alternatives address the critical requirements you need to protect your
virtualized environments. Key requirements for virtualized security include:
- Support the same next-generation firewall features across both physical and
virtual form factors
- Automate the deployment of next-generation firewalls and policies across a
range of virtualization environments
- Isolate and segment mission critical applications and data following Zero
Trust principles
- Stop cyber threats from moving laterally in an east-west manner
- Deliver centralized visibility and policy management for both physical and
virtual form factors
The Palo Alto Networks VM-Series combines next-generation firewall security
and advanced threat prevention to protect your virtualized environments from
advanced cyber threats. Native automation tools such as Virtual Machine
monitoring (VM) and Dynamic Address Groups monitor VM additions,
removals and attribute changes to help eliminate any security policy lag as your
VMs change.
Applying next-generation security to virtualized environments
The VM-Series virtualized firewall is based upon the same full-stack traffic classification engine that can be found in our physical form-factor firewalls. The VM-Series natively classifies all traffic, inclusive of applications, threats and content, and then ties that traffic to the user. The application, content, and user — the elements that run your business — are then used as the basis of your virtualized security policies, resulting in an improved security posture and a reduction in incident response time.
Isolate mission critical applications and data using Zero Trust principles
Security best-practices dictate that your mission-critical applications and data should be isolated in secure segments using Zero Trust (i.e. never trust; always verify) principles at each segmentation point. The VM-Series can be deployed throughout your virtualized environment, residing as a gateway within your virtual network and controlling VM-to-VM communications based on application and user identity. This allows you to control the applications traversing your virtualized environment, while blocking potentially rogue or misconfigured applications and controlling access based on user identity.
Block lateral movement of cyber threats
Today’s cyber threats will commonly compromise an individual workstation or user, and then they will move across the network, looking for a target. Within your virtual network, cyber threats will move laterally from VM-to-VM, in an east-west manner, placing your mission critical applications and data at risk. Exerting application-level control using Zero Trust principles in between VMs will reduce the threat footprint while applying policies to block both known and unknown threats.
Automated, transparent deployment and provisioning
A rich set of automation features and APIs allow customers to streamline their security policy deployment so that security keeps pace with the buildup and teardown of their virtualized mission-critical applications.
- Virtual Machine monitoring: Security policies must be able to monitor and keep up with changes in the virtualization environment, including VM attributes and the addition or removal of VMs. Virtual Machine monitoring (i.e. VM monitoring) automatically polls your virtualization environments for virtual machine inventory and changes, collecting this data in the form of tags that can then be used in dynamic address groups to keep policies up to date.
- Dynamic address groups: As your virtual machines change functions or move from server to server, building security policies based on static data, such as IP address, delivers limited value. dynamic address groups allow you to create policies using tags [from VM monitoring] as an identifier for virtual machines instead of a static object definition. Multiple tags representing virtual machine attributes such as operating system can be resolved within a dynamic address group, allowing you to easily apply policies to virtual machines as they are created or travel across the network.
- RESTful APIs: A flexible, REST-based API allows you to integrate with 3rd party cloud orchestration solutions such as OpenStack and CloudStack. This enables the VM-Series to be deployed and configured in lockstep with virtualized workloads.
- Centralized management: Panorama™ allows you to manage your VM-Series deployments along with your physical security appliances, thereby ensuring policy consistency and cohesiveness. Rich, centralized logging and reporting capabilities provide visibility into virtualized applications, users and content.
Features and Benefits:
Security Features
- Application Visibility
Port numbers, protocols, and IP addresses are useful for network devices, but they tell you nothing about what is on your network. Detailed information about the applications, users, and content traversing your network empowers you to quickly determine any risks they pose and quickly respond. Leveraging the rich context provided by Palo Alto Networks firewalls, our visualization, analysis, and reporting tools let you quickly learn more about activity on your network and analyze incidents from a current or comparative perspective.
- User Visibility
Traditionally, security policies were applied based on IP addresses, but the increasingly dynamic nature of users and applications mean that IP addresses alone have become ineffective as a policy control element for safe application enablement.
- AntiVirus
The broadening use of social media, messaging and other non-work related applications introduce a variety of vectors for viruses, spyware, worms and other types of malware. Palo Alto Networks next-generation firewalls allow you to block unwanted applications with App-ID, and then scan allowed applications for malware.
- IPS
Today's attacks on your network use a combination of application vectors and exploits. Palo Alto Networks next-generation firewalls arm you with a two-pronged approach to stopping these attacks. Unwanted applications are blocked through App-ID, and the applications you choose to allow through are scanned for vulnerability exploits by our NSS-approved IPS engine.
- Data Filtering & File Blocking
The application function level control, file blocking by type, and data filtering features of our next-generation firewalls allow you to implement a range of policies that help balance permitting the use of personal or non-work related applications, with the business and security risks of unauthorized file and data transfer.
- Modern Malware Protection
Modern attackers are increasingly using targeted and new unknown variants of malware to sneak past traditional security solutions. To address this, Palo Alto Networks developed WildFire, which identifies new malware in minutes. By executing suspect files in a virtual environment and observing their behavior, Palo Alto Networks identifies malware quickly and accurately, even if the malware sample has never been seen before. Once a file is deemed malicious, WildFire automatically generates protections that are delivered to all WildFire subscribers within an hour of detection. A WildFire license provides your IT team with a wealth of forensics to see exactly who was targeted, the application used in the delivery, and any URLs that were part of the attack.
- URL Filtering
The perfect complement to the policy-based application control provided by App-ID is our on-box URL filtering database, which gives you total control over related web activity. By addressing your lack of visibility and control from both an application and web perspective, App-ID and URL Filtering together protect you from a full spectrum of legal, regulatory, productivity, and resource utilization risks.
- Mobile Security
Mobile devices are a part of nearly every modern network. As a result, security teams need to deliver protection and policy enforcement to a myriad of new devices and applications. The Palo Alto Networks next-generation firewall extends comprehensive application visibility and control and vulnerability protection to mobile devices.
Networking Features
- Decryption
Take control of your SSL and SSH encrypted traffic and ensure it is not being used to conceal unwanted activity or dangerous content. Using policy-based decryption and inspection, you can confirm that SSL and SSH are being used for business purposes only, instead of to spread threats or unauthorized data transfer.
- IPv6
Our next-generation firewalls allow you to deploy consistent, safe application enablement policies across IPv6, IPv4 and mixed environments.
- Networking
Our flexible networking architecture includes dynamic routing, switching, and VPN connectivity, which enables you to easily deploy Palo Alto Networks next-generation firewalls into nearly any networking environment.
- VPN
Secure site-to-site and remote user connectivity is a critical infrastructure component. Every Palo Alto Networks next-generation firewall platform allows you to easily and securely communicate between sites using standards-based IPSec VPN connections. Remote user communications are protected through a rich set of VPN features.
- Virtualization Security
To optimize computing resources, enterprises are moving towards supporting virtualized applications with different risk levels on a single server. In these environments, virtualized firewalls are critical to deliver security for your communications within the virtualized server.
Management Features
- Device Management
Our firewall management philosophy is to make administrative tasks such as report generation, log queries, policy creation, and ACC browsing easy to execute and consistent, no matter which mechanism - web interface, Panorama, CLI or API - you use.
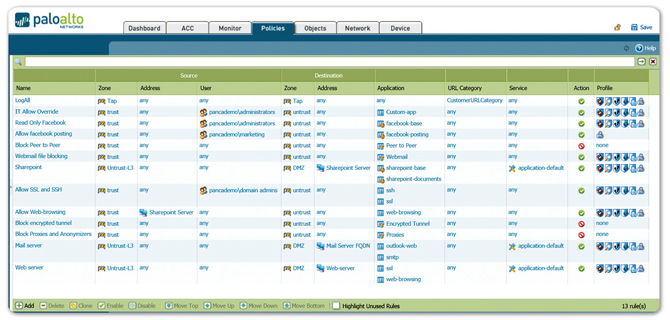
- Policy Control
The increased visibility into applications, users and content delivered by Palo Alto Networks simplifies figuring out which applications are traversing your network, who is using them, and the potential security risks. Armed with this data, you can apply secure enablement policies with a range of responses that are more finely tuned than the traditional 'allow or deny' approach.
- Redundancy
Palo Alto Networks next-generation firewalls support a series of redundancy and resiliency features that ensure your firewall will continue to provide the secure application enablement you need to keep your business running.
- Virtual Systems
Virtual systems are unique and distinct next-generation firewall instances within a single Palo Alto Networks firewall. Instead of deploying many individual firewalls, security service providers and enterprises can deploy a single pair of firewalls (high availability) and enable a series of virtual firewall instances (virtual systems). Each virtual system is an independent (virtual) firewall within your firewall that is managed separately and cannot be accessed or viewed by other users.
Deployment Flexibility:
The VM-Series can be deployed in a variety of hypervisor and orchestration environments:
VM-Series for ESXi (standalone):
The VM-Series on ESXi servers is ideal for networks where the virtual form factor may simplify deployment and provide more flexibility. Common deployment scenarios include:
- Private or public cloud computing environments where virtualization is a dependency
- Environments where physical space is at a premium
- Remote locations where shipping hardware is not practical
The VM-Series for ESXi supports a range of interface types including L2, L3 and virtual wire, allowing you to deploy the VM-Series in a different interface mode for each virtualized server, depending on your needs.
VM-Series for VMware NSX
The VM-Series for NSX automates the provisioning and deployment of next-generation firewalls and advanced threat prevention by tightly integrating the VM-Series, Panorama for centralized management, and VMware NSX network virtualization. VMware NSX automatically directs application traffic and associated content to the VM-Series for analysis and inspection. Panorama enables you to define applicationbased security policies and create dynamic address groups, which include virtual machine attributes such as IP address and operating system, allowing you to dynamically apply policies to virtual machines as they are created or travel across the network. Please see the VM-Series for VMware NSX solution brief for more information on this integration.
VM-Series for Citrix SDX
The VM-Series on Citrix NetScaler SDX enables security and application delivery controller (ADC) capabilities to be consolidated on a single platform, delivering a comprehensive set of cloud-based services to enhance the availability, security and performance of applications. This integrated solution addresses the independent application needs for business units, owners and service provider customers in a multi-tenant deployment. In addition, this combined offering provides a complete, validated, security and ADC solution for Citrix XenApp and XenDesktop deployments. Please see the VM-Series for Citrix SDX solution brief for more information on this integration.
VM-Series for Amazon Web Services
The VM-Series for Amazon Web Services (AWS) enables you to protect public cloud deployments with our next-generation firewall and advanced threat prevention capabilities. Available as an Amazon Machine Interface (AMI), the VM-Series can be deployed as an EC2 instance to protect traffic flowing into and across your VPC. A rich set of automation features enable security policy deployment to keep pace with changes in your VPC. Panorama enables you to centrally manage all of your Palo Alto Networks deployments. Please see the VM-Series for AWS solution brief for more information on this integration.
VM-Series for KVM
The VM-Series for Kernel Virtual Machine (KVM) will allow service providers and enterprises alike to add next-generation firewall and advanced threat prevention capabilities to their Linux-based virtualization and cloud-based initiatives. KVM is a popular open-source hypervisor that will enable service providers and enterprises to deploy and manage the VM-Series across a range of Linux operating systems including CentOS/ RHEL and Ubuntu. In addition to the rich set of automation features and APIs within the VM-Series, the VM-Series for KVM can be managed using Panorama, along with the optional support for the OpenStack plugin. Please see the VM-Series for KVM solution brief for more information on this integration.
Next-Generation Firewall Solutions:
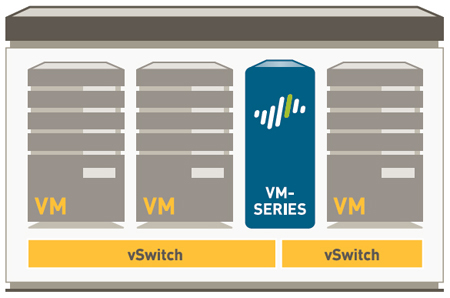
Fundamental shifts in the application and threat landscape, user behavior, and network infrastructure have steadily eroded the security that traditional port-based firewalls once provided. Your users are accessing all types of applications using a range of device types, often times to get their job done. Meanwhile, datacenter expansion, virtualization, mobility, and cloud-based initiatives are forcing you to re-think how to enable application access yet protect your network.
Traditional responses include an attempt to lock down all application traffic through an evergrowing list of point technologies in addition to the firewall, which may hinder your business; or allowing all applications, which is equally unacceptable due to increased business and security risks. The challenge that you face is that your traditional port-based firewall, even with bolt-on application blocking, does not provide an alternative to either approach. In order to strike a balance between allowing everything and denying everything, you need to safely enable applications by using business-relevant elements such as the application identity, who is using the application, and the type of content as key firewall security policy criteria.
Key safe enablement requirements:
- Identify applications, not ports. Classify traffic, as soon as it hits the firewall, to determine the application identity, irrespective of protocol, encryption, or evasive tactic. Then use that identity as the basis for all security policies.
- Tie application usage to user identity, not IP address, regardless of location or device. Employ user and group information from enterprise directories and other user stores to deploy consistent enablement policies for all your users, regardless of location or device.
- Protest against all threats—both known and unknown. Prevent known vulnerability exploits, malware, spyware, malicious URLs while analyzing traffic for, and automatically delivering protection against highly targeted and previously unknown malware.
- Simplify policy management. Safely enable applications and reduce administrative efforts with easy-to-use graphical tools, a unified policy editor, templates, and device groups.
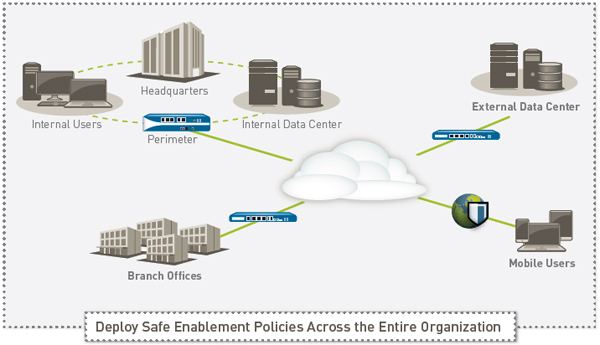
Safe application enablement policies can help you improve your security posture, regardless of the deployment location. At the perimeter, you can reduce your threat footprint by blocking a wide range of unwanted applications and then inspecting the allowed applications for threats— both known and unknown. In the datacenter – traditional or virtualized, application enablement translates to ensuring only datacenter applications are in use by authorized users, protecting the content from threats and addressing security challenges introduced by the dynamic nature of the virtual infrastructure. Your enterprise branch offices and remote users can be protected by the same set of enablement policies deployed at the headquarters location, thereby ensuring policy consistency.
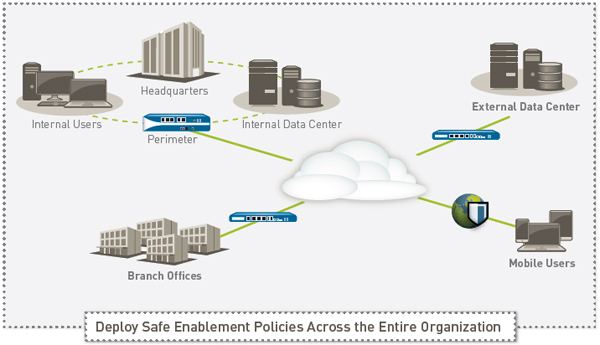
Enabling Applications to Empower the Business
Safe application enablement with Palo Alto Networks™ next-generation firewalls helps you address your business and security risks associated with the rapidly growing number of applications traversing your network. By enabling applications for users or groups of users, both local, mobile, and remote, and protecting the traffic against known and unknown threats, you can improve your security posture while growing your business.
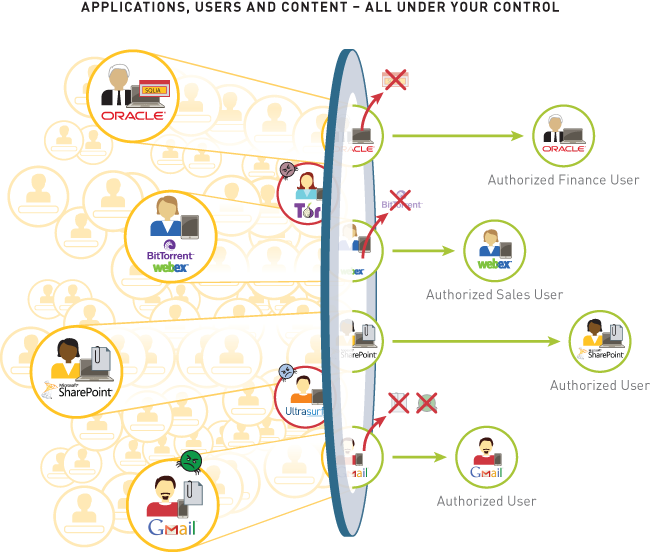
- Classifying all applications, across all ports, all the time. Accurate traffic classification is the heart of any firewall, with the result becoming the basis of the security policy. Today, applications can easily bypass a port-based firewall; hopping ports, using SSL and SSH, sneaking across port 80, or using non-standard ports. App-ID™ addresses the traffic classification visibility limitations that plague traditional firewalls by applying multiple classification mechanisms to the traffic stream, as soon as the firewall sees it, to determine the exact identity of application traversing your network, regardless of port, encryption (SSL or SSH) or evasive technique employed. The knowledge of exactly which applications are traversing your network, not just the port and protocol, becomes the basis for all your security policy decisions. Unidentified applications, typically a small percentage of traffic, yet high in potential risk, are automatically categorized for systematic management— which can include policy control and inspection, threat forensics, creation of a custom App-ID, or a packet capture for Palo Alto Networks App-ID development.
- Integrating users and devices, not just IP addresses into policies. Creating and managing security policies based on the application and the identity of the user, regardless of device or location, is a more effective means of protecting your network than relying solely on port and IP address. Integration with a wide range of enterprise user repositories provides the identity of the Microsoft Windows, Mac OS X, Linux, Android, or iOS user accessing the application. Users who are traveling or working remotely are seamlessly protected with the same, consistent policies that are in use on the local, or corporate network. The combined visibility and control over a user's application activity means you can safely enable the use of Oracle, BitTorrent, or Gmail, or any other application traversing your network, no matter where or how the user is accessing it.
- Protect against all threats, both known and unknown. To protect today's modern network, you must address a blend of known exploits, malware and spyware as well as completely unknown and targeted threats. This process begins by reducing the network attack surface by allowing specific applications and denying all others, either implicitly through a deny-all-else strategy or through explicit policies. Coordinated threat prevention can then be applied to all allowed traffic, blocking known malware sites, vulnerability exploits, viruses, spyware and malicious DNS queries in a single pass. Custom or otherwise unknown malware is actively analyzed and identified by executing the unknown files and directly observing more than 100 malicious behaviors in a virtualized sandbox environment. When new malware is discovered, a signature for the infecting file and related malware traffic is automatically generated and delivered to you. All threat prevention analysis uses full application and protocol context, ensuring that threats are always caught even if they attempt to hide from security in tunnels, compressed content or on non-standard ports.
Deployment and Management Flexibility
Safe application enablement functionality is available in either a purpose-built hardware platform or in a virtualized form factor. When you deploy multiple Palo Alto Networks firewalls, in either hardware or virtual form factors, you can use Panorama, an optional centralized management offering to gain visibility into traffic patterns, deploy policies, generate reports and deliver content updates from a central location.
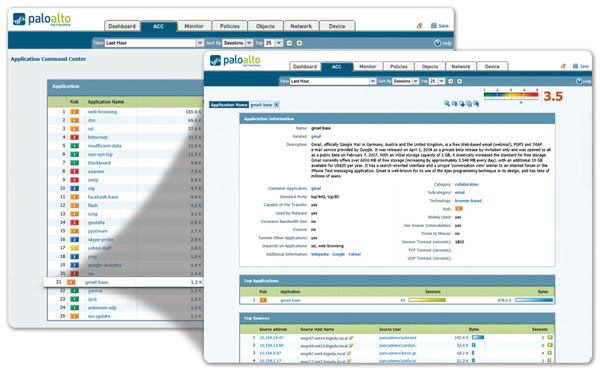
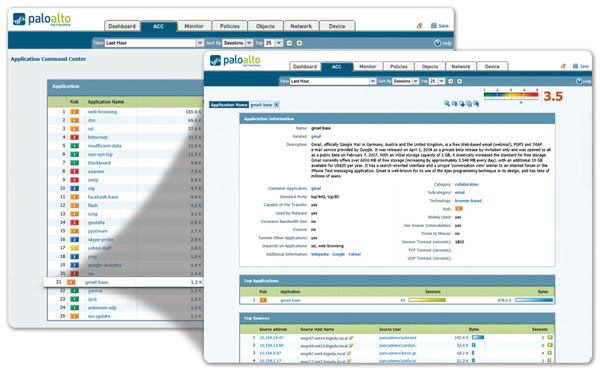
Application Visibility: View application activity in a clear, easy-to-read format. Add and remove filters to learn more about the application, its functions and who is using them.
Safe Application Enablement: A Comprehensive Approach
Safe application requires a comprehensive approach to securing your network and growing your business that begins with in-depth knowledge of the applications on your network; who the user is, regardless of their platform or location; what content, if any, the application is carrying. With more complete knowledge of network activity, you can create more meaningful security policies that are based on elements of application, user and content that are relevant to your business. The user location, their platform and where the policy is deployed—perimeter, traditional or virtualized datacenter, branch office or remote user— make little or no difference to how the policy is created. You can now safely enable any application, any user, and any content.
Complete Knowledge Means Tighter Security Policies
Security best practices dictate that more complete knowledge of what's on your network is beneficial to implementing tighter security policies. For example, knowing exactly which applications are traversing your network, as opposed to the broader set of traffic that is portbased, enables your administrators to specifically allow the applications that enable your business while blocking, unwanted applications. The knowledge of who the user is, not just their IP address, adds another policy criteria that allows you to be more specific in your policy assignment.
- Using a powerful set of graphical visualization tools, your administrators can gain a more complete picture of the application activity, the potential security impact, and make a more informed policy decision. Applications are continuously classified and as their state changes, the graphical summaries are dynamically updated, displaying the information in an easy-touse, web-based interface.
- New or unfamiliar applications can be quickly investigated with a single click that displays a description of the application, its behavioral characteristics, and who is using it.
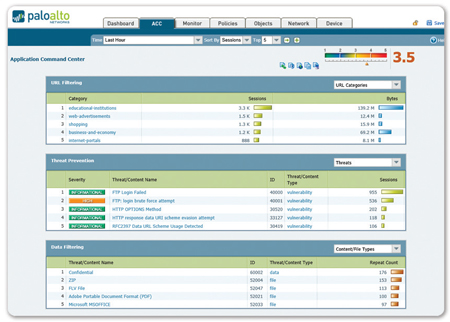
- Additional visibility into URL categories, threats, and data patterns provides a complete and well-rounded picture of network activity.
- Unknown applications, typically a small percentage on every network, yet high in potential risk, are categorized for analysis to determine if they are internal applications, as yet unidentified commercial applications, or threats.
Enabling Applications and Reducing Risk
Safe application enablement uses policy decision criteria that includes application/application function, users and groups, and content as a means of striking a balance between business limiting denying of all applications and the high risk alternative of allowing all applications.
At the perimeter, including branch offices, mobile, and remote users, enablement policies are focused on identifying all the traffic, then selectively allowing the traffic based on user identity; then scanning the traffic for threats. Policy examples may include:
- Limit the use of webmail and instant messaging usage to a select few variants; decrypt those that use SSL, inspect the traffic for exploits and upload unknown files to WildFire™ for analysis and signature development.
- Allow streaming media applications and websites but apply QoS and malware prevention to limit the impact on VoIP applications and protect your network.
- Control Facebook by allowing all your users to "browse", blocking all Facebook games and social plugins; and allowing Facebook posting only for marketing. Scan all Facebook traffic for malware and exploits
- Control web-surfing by allowing and scanning traffic to business related web sites while blocking access to obvious non-work related web sites; "coach" access to questionable sites through customized block pages.
- Enforce consistant security by transparently deploying the same policies to all users, local, mobile, or remote, with GlobalProtect™.
- Use an implicit deny-all-else strategy or explicitly block unwanted applications such as P2P and circumventors or traffic from specific countries to reduce the application traffic that introduces business and security risk.
In the datacenter—traditional, virtualized or a combination thereof—enablement examples are focused on confirming applications, looking for rogue applications, and protecting the data.
- Isolate the Oracle-based credit card number repository in its own security zone; control access to finance groups, forcing the traffic across its standard ports, and inspecting the traffic for application vulnerabilities.
- Enable only the IT group to access the datacenter using a fixed set of remote management applications (e.g., SSH, RDP, Telnet) across their standard ports.
- Allow Microsoft SharePoint Administration to be used by only your administration team, and allow access to Microsoft SharePoint Documents for all other users.
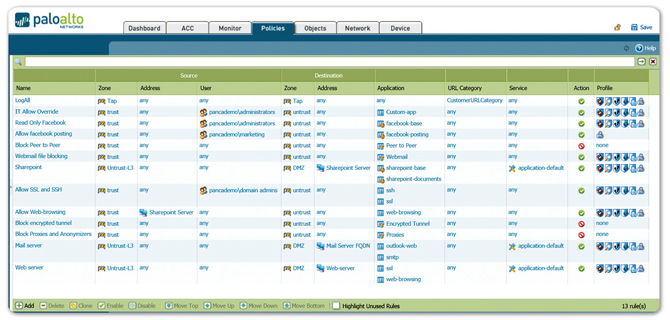
Unified Policy Editor: A familiar look and feel enables the rapid creation and deployment of policies that control applications, users and content.
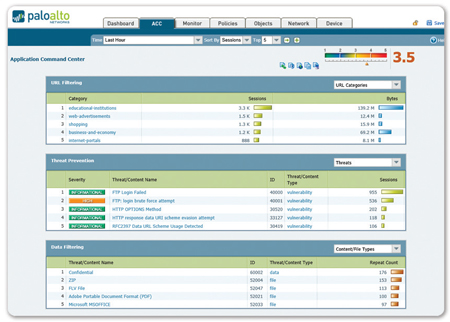
Content and Threat Visibility: View URL, threat and file/data transfer activity in a clear, easy-to-read format. Add and remove filters to learn more about individual elements.
Protecting Enabled Applications
Safe application enablement means allowing access to certain applications, then applying specific policies to block known exploits, malware and spyware – known or unknown; controlling file or data transfer, and web surfing activity. Common threat evasion tactics such as port-hopping and tunneling are addressed by executing threat prevention policies using the application and protocol context generated by the decoders in App-ID. In contrast, UTM solutions take a silo-based approach to threat prevention, with each function, firewall, IPS, AV, URL filtering, all scanning traffic without sharing any context, making them more susceptible to evasive behavior.
- Block Known Threats: IPS and Network Antivirus/Anti-spyware. A uniform signature format and a stream-based scanning engine enables you to protect your network from a broad range of threats. Intrusion prevention system (IPS) features block network and application-layer vulnerability exploits, buffer overflows, DoS attacks, and port scans. Antivirus/Anti-spyware protection blocks millions of malware variants, as well as any malware-generated command-and-control traffic, PDF viruses, and malware hidden within compressed files or web traffic (compressed HTTP/HTTPS). Policy-based SSL decryption across any application on any port protects you against malware moving across SSL encrypted applications.
- Block Unknown, Targeted Malware: Wildfire. Unknown or targeted malware is identified and analyzed by WildFire, which directly executes and observes unknown files in a cloud-based, virtualized sandbox environment. WildFire monitors for more than 100 malicious behaviors and the result is delivered immediately to the administrator in the form of an alert. An optional WildFire subscription offers enhanced protection, logging, and reporting. As a subscriber, you are protected within an hour when a new piece of malware is found anywhere in the world, effectively stopping the spread of new malware before it impacts you. As a subscriber, you also gain access to integrated WildFire logging and reporting and an API for submitting samples to the WildFire cloud for analysis.
- Identify Bot-Infected Hosts. App-ID classifies all applications, across all ports, including any unknown traffic, which can often expose anomalies or threats in your network. The behavioral botnet report correlates unknown traffic, suspicious DNS and URL queries and a variety of unusual network behaviors to reveal devices that are likely infected with malware. The results are displayed in the form of a list of potentially infected hosts that can be investigated as possible members of a botnet.
- Limit Unauthorized File and Data Transfers. Data filtering features enable your administrators to implement policies that will reduce the risks associated with unauthorized file and data transfers. File transfers can be controlled by looking inside the file (as opposed to looking only at the file extension), to determine if the transfer action should be allowed or not. Executable files, typically found in drive-by downloads, can be blocked, thereby protecting your network from unseen malware propagation. Data filtering features can detect, and control the flow of confidential data patterns (credit card or social security numbers as well as custom patterns).
- Control Web Surfing. A fully-integrated, customizable URL filtering engine allows your administrators to apply granular web-browsing policies, complementing application visibility and control policies and safeguarding the enterprise from a full spectrum of legal, regulatory, and productivity risks. In addition, the URL categories can be leveraged into the policies to provide further granularity of control for SSL decryption, QoS, or other rule bases.
Ongoing Management and Analysis
Security best practices dictate that your administrators strike a balance between proactively managing the firewall, whether it is a single device or many hundreds, and being reactive, investigating, analyzing, and reporting on security incidents.
- Management: Each Palo Alto Networks platform can be managed individually via a command line interface (CLI) or full-featured browser-based interface. For large-scale deployments, Panorama can be licensed and deployed as a centralized management solution that enables you to balance global, centralized control with the need for local policy flexibility using features such as templates and shared policy. Additional support for standards-based tools such as SNMP, and REST-based APIs allow you to integrate with third-party management tools. Whether using the device's web interface or Panorama's, the interface look and feel is identical, ensuring that there is no learning curve when moving from one to another. Your administrators can use any of the provided interfaces to make changes at any time without needing to worry about synchronization issues. Role-based administration is supported across all management mediums, allowing you to assign features and functions to specific individuals.
- Reporting: Predefined reports can be used as-is, customized, or grouped together as one report in order to suit the specific requirements. All reports can be exported to CSV or PDF format and can be executed and emailed on a scheduled basis.
- Logging: Real-time log filtering facilitates rapid forensic investigation into every session traversing your network. Log filter results can be exported to a CSV file or sent to a syslog server for offline archival or additional analysis.
Purpose-Built Hardware or Virtualized Platforms
Palo Alto Networks offers a full line of purpose-built hardware platforms that range from the PA-200, designed for enterprise remote offices to the PA-5060, which is designed for high-speed datacenters. The platform architecture is based on a single pass software engine and uses function specific processing for networking, security, threat prevention and management to deliver you predictable performance. The same firewall functionality that is delivered in the hardware platforms is also available in the VM-Series virtual firewall, allowing you to secure your virtualized and cloud-based computing environments using the same policies applied to your perimeter or remote office firewalls.
Technical Specifications:
| Model |
VM-100 |
VM-200 |
VM-300 |
VM-1000-HV |
| Max sessions |
50,000 |
100,000 |
250,000 |
250,000 |
| IPSec VPN tunnels/tunnel interfaces |
25 |
500 |
2,000 |
2,000 |
| GlobalProtect (SSL VPN) concurrent users |
25 |
200 |
500 |
500 |
| SSL decrypt sessions |
1024 |
1024 |
1024 |
12,500 |
| SSL inbound certificates |
25 |
25 |
25 |
1,000 |
| Virtual routers |
3 |
3 |
3 |
3 |
| Security zones |
10 |
20 |
40 |
40 |
| Max number of policies |
250 |
2,000 |
5,000 |
10,000 |
| Address objects |
2,500 |
4,000 |
10,000 |
10,000 |
| Firewall throughput (App-ID Enabled) |
1 Gbps |
1 Gbps |
1 Gbps |
1 Gbps |
| Threat prevention throughput |
600 Mbps |
600 Mbps |
600 Mbps |
600 Mbps |
| IPSec VPN throughput |
250 Mbps |
250 Mbps |
250 Mbps |
250 Mbps |
| New sessions per second |
8,000 |
8,000 |
8,000 |
8,000 |
| HyperVisor |
VMware ESXi 4.1 and ESXi 5.0 |
| Network driver |
VMXNet3 |
| CPU cores |
2, 4 or 8 |
| Memory (Minimum) |
4GB |
| Disk drive capacity (Min/Max) |
40GB/2TB |
Networking Specifications:
Interface Modes
- L2, L3, Tap, Virtual wire (transparent mode)
Routing
- Modes: OSPF, RIP, BGP, Static
- Forwarding table size (entries per device/per VR): 5000/5000 (VM-300), 1,250/1,250 (VM-200), 1000/1000 (VM-100)
- Policy-based forwarding
- Multicast: PIM-SM, PIM-SSM, IGMP v1, v2, and v3
High-Availability
- Modes: Active/Passive with no session synchronization
- Failure detection: Path monitoring, Interface monitoring
Address Assignment
- Address assignment for device: DHCP Client/PPPoE/Static
- Address assignment for users: DHCP Server/DHCP Relay/Static
IPV6
- Features: L2, L3, Tap, Virtual Wire (transparent mode)
- Services: App-ID, User-ID, Content-ID, WildFire and SSL Decryption
|
VLANS
- 802.1q VLAN tags per device/per interface: 4,094/4,094
- Max interfaces: 2,000 (VM-300), 500 (VM-200), 100 (VM-100)
NAT/PAT:
- Max NAT rules: 1,000 (VM-300), 1,000 (VM-200), 125 (VM-100)
- Max NAT rules (DIPP): 200 (VM-300), 200 (VM-200), 125 (VM-100)
- Dynamic IP and port pool: 254
- Dynamic IP pool: 32,000
- NAT Modes: 1:1 NAT, n:n NAT, m:n NAT
- DIPP oversubscription (Unique destination IPs per source port and IP): 2 (VM-300), 1 (VM-200), 1 (VM-100)
- NAT64
Virtual Wire
- Max virtual wires: 1,000 (VM-300), 250 (VM-200), 50 (VM-100)
- Interface types mapped to virtual wires: physical and subinterfaces
L2 Forwarding
- ARP table size/device: 2,500 (VM-300), 500 (VM-200), 500 (VM-100)
- MAC table size/device: 2,500 (VM-300), 500 (VM-200), 500 (VM-100)
- IPv6 neighbor table size: 1,000 (VM-300), 500 (VM-200), 500 (VM-100)
|
Security Specifications:
Firewall
- Policy-based control over applications, users and content
- Fragmented packet protection
- Reconnaissance scan protection
- Denial of Service (DoS)/Distributed Denial of Services (DDoS) protection
- Decryption: SSL (inbound and outbound), SSH
Wildfire
- Identify and analyze targeted and unknown files for more than 100 malicious behaviors
- Generate and automatically deliver protection for newly discovered malware via signature updates
- Signature update delivery in less than 1 hour, integrated logging/reporting; access to WildFire API for programmatic submission of up to 100 samples per day and up to 1,000 report queries by file hash per day (Subscription Required)
File and Data Filtering
- File transfer: Bi-directional control over more than 60 unique file types
- Data transfer: Bi-directional control over unauthorized transfer of CC# and SSN
- Drive-by download protection
User Integration (User-ID)
- Microsoft Active Directory, Novell eDirectory, Sun One and other LDAP-based directories
- Microsoft Windows Server 2003/2008/2008r2, Microsoft Exchange Server 2003/2007/2010
- Microsoft Terminal Services, Citrix XenApp
- XML API to facilitate integration with non-standard user repositories
IPSEC VPN (Site-To-Site)
- Key Exchange: Manual key, IKE v1
- Encryption: 3DES, AES (128-bit, 192-bit, 256-bit)
- Authentication: MD5, SHA-1, SHA-256, SHA-384, SHA-512
- Dynamic VPN tunnel creation (GlobalProtect)
|
Threat Prevention (Subscription Required)
- Application, operating system vulnerability exploit protection
- Stream-based protection against viruses (including those embedded in HTML, Javascript, PDF and compressed), spyware, worms
URL Filtering (Subscription Required)
- Pre-defined and custom URL categories
- Device cache for most recently accessed URLs
- URL category as part of match criteria for security policies
- Browse time information
Quality of Service (QOS)
- Policy-based traffic shaping by application, user, source, destination, interface, IPSec VPN tunnel and more
- 8 traffic classes with guaranteed, maximum and priority bandwidth parameters
- Real-time bandwidth monitor
- Per policy diffserv marking
- Physical interfaces supported for QoS: 6 (VM-300, VM-200), 4(VM-100)
SSL VPN/Remote Access (GlobalProtect)
- GlobalProtect Gateway
- GlobalProtect Portal
- Transport: IPSec with SSL fall-back
- Authentication: LDAP, SecurID, or local DB
- Client OS: Mac OS X 10.6, 10.7 (32/64 bit), 10.8 (32/64 bit), Windows XP, Windows Vista (32/64 bit), Windows 7 (32/64 bit)
- Third party client support: Apple iOS, Android 4.0 and greater, VPNC IPSec for Linux
Management, Reporting, Visibility Tools
- Integrated web interface, CLI or central management (Panorama)
- Multi-language user interface
- Syslog, SNMP v2/v3
- XML-based REST API
- Graphical summary of applications, URL categories, threats and data (ACC)
- View, filter and export traffic, threat, WildFire, URL, and data filtering logs
- Fully customizable reporting
|
*Performance and capacities are measured under ideal testing conditions using PAN-OS 5.0 and 4 CPU cores.